Users need to own their Identity
In the digital age, our identities are increasingly intertwined with online platforms, social media accounts, and various online services. However, this convenience comes at a cost—our personal information is scattered across numerous centralized databases, vulnerable to security breaches and privacy violations. As the risks of identity theft and data misuse grow, a paradigm shift toward decentralized identity and self-sovereign identity (SSI) is gaining momentum. This blog post delves into the importance of users owning their identity in this decentralized landscape.
Taking Control of Personal Data:
Decentralized identity puts the control back into the hands of individuals. Traditionally, our personal data is stored on servers controlled by organizations, exposing us to potential data breaches. With self-sovereign identity, individuals hold their own personal information, which is cryptographically secured and shared only on a need-to-know basis. By owning their identity, users gain greater control over their personal data, deciding how and when it is shared (Daher, 2019).
Enhanced Privacy and Security:
In a centralized system, user data is concentrated, making it an attractive target for hackers and malicious actors. Breaches can have severe consequences, leading to identity theft, financial loss, and reputational damage. Decentralized identity mitigates these risks by distributing data across a network of interconnected nodes, reducing the vulnerability of a single point of failure. Cryptographic protocols ensure that personal information remains private and secure, enabling users to authenticate themselves without revealing unnecessary details (Hardt, 2019).
Interoperability and Portability:
Today, individuals have multiple online identities across various platforms. Each platform typically operates in silos, making it challenging to manage and authenticate identities seamlessly. Decentralized identity introduces interoperability and portability, allowing users to manage a unified digital identity across multiple services. With a portable identity, individuals can effortlessly navigate through different applications, eliminating the need for separate accounts and redundant data entry (W3C, 2021).
Empowering User Consent and Control:
Centralized systems often operate under opaque data practices, where users have limited control over their data and how it is utilized. In contrast, self-sovereign identity empowers individuals by providing granular control over data sharing. Users can define the extent and purpose of data access, ensuring informed consent and reducing the risk of data misuse. This newfound agency fosters trust between users and service providers, forming the foundation for a more transparent and user-centric digital ecosystem (ConsenSys, 2018).
Successful Implementations:
Several companies have successfully adopted decentralized identity solutions. One prominent example is Microsoft, which has developed the Microsoft Authenticator app that allows users to store and manage their digital identities securely. The app employs decentralized identifiers (DIDs) and verifiable credentials, enabling users to control their personal information and share it selectively with others (Microsoft, 2021).
Another notable example is Sovrin, an open-source project that provides a decentralized identity network. Sovrin aims to create a global public utility for self-sovereign identity, allowing individuals and organizations to manage their identities without relying on centralized authorities. Its architecture is designed to protect privacy, ensure security, and enable trust in online interactions (Sovrin Foundation, n.d.).
Resources
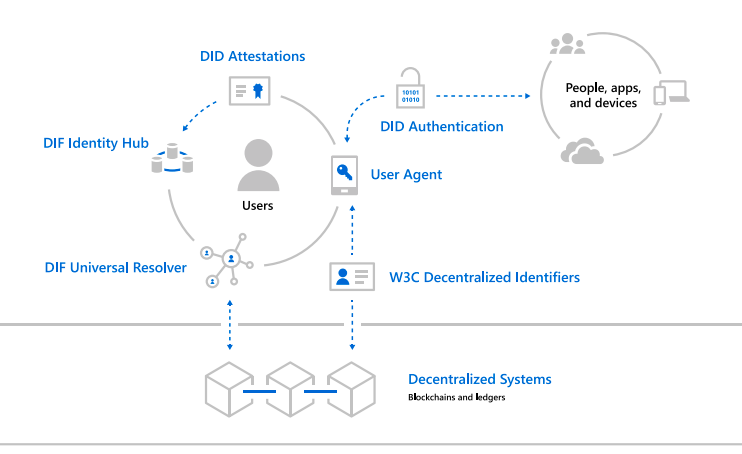
The Decentralized Identity Foundation (DIF) with individuals and organizations who are similarly motivated to take on this challenge. We are building on top of the standards established by the DIF and are using the following constructs in our infrastructure
– Decentralized Identifiers (DIDs) – a W3C spec that defines a common document format for describing the state of a Decentralized Identifier
– Identity Hubs – an encrypted identity datastore that features message/intent relay, attestation handling, and identity-specific compute endpoints.
– Universal DID Resolver – a server that resolves DIDs across blockchains
– Verifiable Credentials – a W3C spec that defines a document format for encoding DID-based attestations.
Conclusion:
The shift towards decentralized identity and self-sovereign identity marks a transformative era in the digital landscape. By enabling users to own their identities, we unlock a myriad of benefits—control over personal data, enhanced privacy and security, interoperability, user consent, and inclusion. As individuals, organizations, and governments recognize the significance of user-centric identity solutions, we move closer to a future where individuals have greater agency over their digital lives, fostering
Summarizing the future as we see it
– Uses Own and control their Identity.
– Privacy by design, built in from the ground up.
– Trust is earned and attested by individuals and systems that need to trust them
– Identity operates with Open and Interoperable Standards